What are cross-site scripting (XSS) attacks?
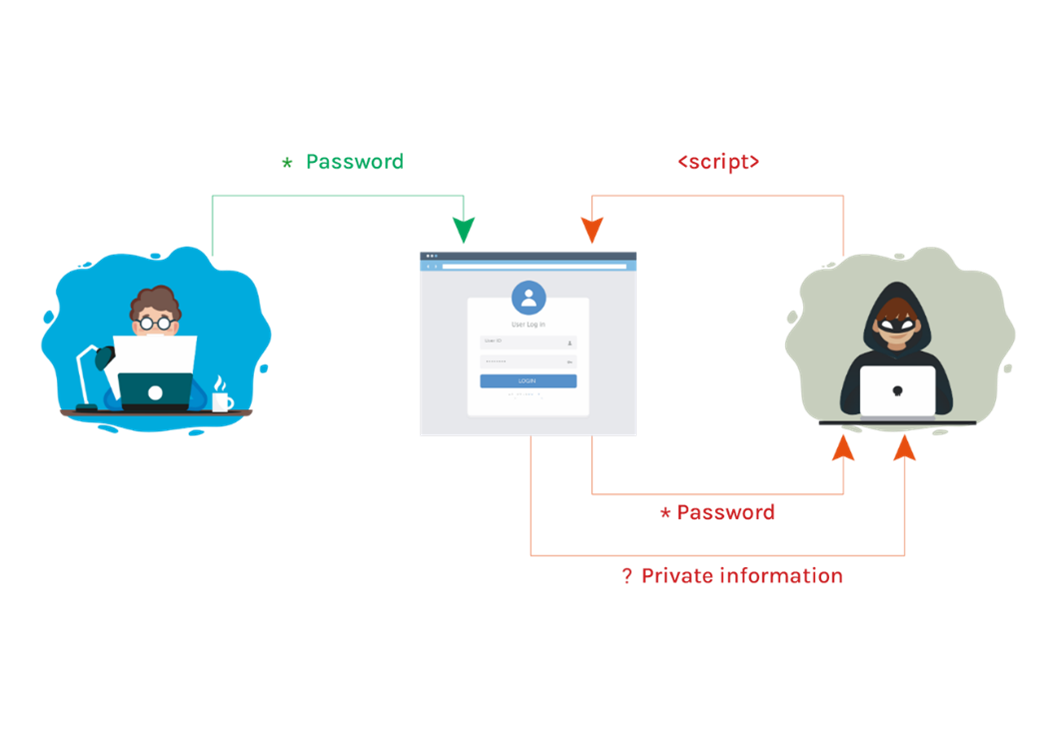
During a cross-site scripting (XSS) attack, cybercriminals inject code into your website to perform actions such as redirecting users to a malicious website or stealing passwords.
Case study:
In 2018, British Airways suffered an XSS attack in which the banking details of more than 400,000 customers were intercepted.
In the same year, one of Ticketmaster's suppliers suffered a similar attack, leaking the data of 40,000 Ticketmaster customers.
If a cybercriminal performs a successful cross site scripting (XSS) attack on your website, it allows them to perform many actions on your website. For example, they can see any kind of information that is transmitted to your website (such as personal and payment information), even if you have SSL encryption in place.
Even if your website does not allow users to enter data or it is solely focused on marketing only, cross-site scripting attacks could cause users to be redirected to fake pages where cybercriminals can perform other malicious activities such as installing malware (malicious software).
Protecting yourself from cross-site scripting (XSS) attacks requires changes to your website that would normally be easily implemented by a computer scientist or developer (but would be difficult for a non-technical person to implement). These changes include adding Content-Type and X-Content-Type-Options headers to your website and creating a Content Security Policy (CSP).
Please refer to the "Website Security" section of the platform to learn about your protection against cross-site scripting and send the technical report to your web developer to fix any vulnerabilities found.